“Virtual Machines and Containers differ in several ways, but the main difference is that containers provide virtualization, so that multiple workloads can run on a single OS instance.”
Imagine a ship carrying cars wrapped with different layers of packaging materials. Now imagine that same ship, but the cars are not wrapped and are just stacked on top of each other. Which ship would be more efficient?
The answer is obvious: The ship carrying the packaged cars. This is the same idea when it comes to software containers. That’s because containers are a more efficient way to package and transport goods, so the “cars” (as used in this example) are less likely to be damaged during transit.
Containers and Virtual Machines (VMs) are both ways to package software so it can be run in different environments. But while VMs virtualize the underlying software, containers virtualize the operating system, meaning each container can only hold one application and its libraries.
In computing, virtualization is the creation of a virtual — as opposed to a physical — version of computer hardware platforms, storage devices, and network resources. Virtualization creates virtual resources from physical resources, like hard drives, Central Processing Units (CPUs), and Graphic Processing Units (GPUs). By virtualizing resources, you can combine a network of resources into what appears to users as one object. For example, you can store data from one or multiple sources on a network of hard drives that appears to users as a singular drive.
Virtualization is the technology on which many popular development tools like Containers and Virtual Machines (VMs) are built. Organizations worldwide depend on the security, accessibility, and flexibility of virtualization made possible through these tools.
What Is A Container
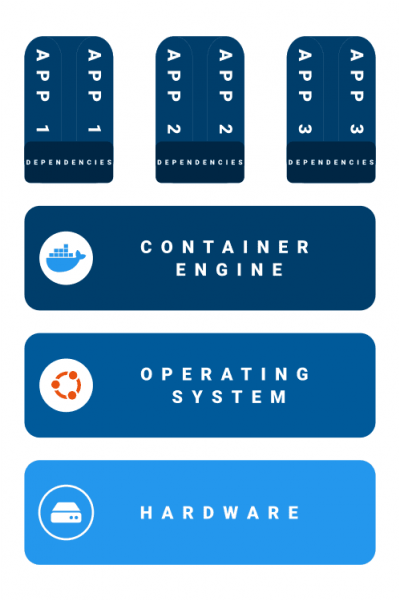
There are two types of containers: application containers and system containers. System containers are much less common now, but were popular before Docker made containers commonplace in 2015. Generally, people discussing containers mean application containers.
A Container is a process or group of processes isolated from other programs on a shared kernel. A kernel is a computer program at the core of a computer’s operating system (OS) and generally has complete control over everything in the system. Containers are a guest OS with virtual resources. Containers do not have awareness of other processes running on the host OS. Unlike a host OS, which has direct access to hardware, a guest OS has limited access to hardware, just like any other application running on the host OS.
Containers are built from read-only templates called images that are pulled from a central repository to run on a host machine.
Typically, containers run a single process or application, although they can handle more than one. Containers usually run on Linux machines, where they run in a separate namespace. These containers are neither dependent on nor directly interacting with other processes on the machine running them. Implementations on other operating systems follow similar architectural principles. Any communication between the container and other processes and devices is through additional interfacing software.
Although Containers encapsulate the files and binaries they need to run, they require a container engine on which to run. There are several essential tools that allow users to manage and create containers quickly.
Docker, the most popular container system, uses a daemon to create and manage containers. Other container systems like Buildah and Kaniko offer daemon-less architecture. Daemon-less container building may offer greater security because Buildah and Kaniko do not need root access for their full functionality. However, these tools alone cannot run or manage containers. Developers may prefer tools like Docker and Podman because they let users build images and run and configure containers.
Containers are useful because they are highly portable. Most common container engines run in multiple environments and are lightweight in resource use. Because containers package all the dependencies they need, they run consistently regardless of what compatible system you implement them on. That means that once you build an application from one or multiple containers, you can implement it on many different systems.
This portability makes containers perfect for large organizations that require computer networks to run identical software. Containers are also used to conduct parallel tests as a part of a continuous integration and continuous deployment (CI/CD) pipeline. Containers can also run repeated tasks simultaneously and divide individual processes of a larger application into individual Microservices.
What Is A Virtual Machine (VM)
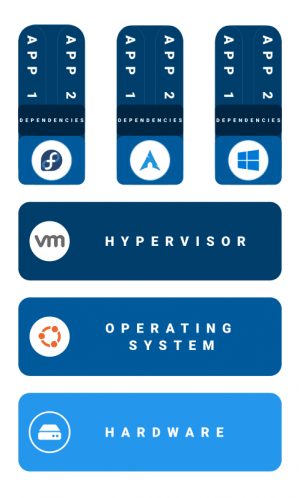
Like a container, a VM is a piece of software used for virtualization. But unlike containers, you must build VMs on top of a software layer called a hypervisor. While a container is an isolated process made for a single service, VMs run a whole and separate OS. That means that a single VM can handle a wide range of tasks and execute them all simultaneously, and can be used for a broader set of use cases.
Because VMs create a complete computing environment, you can install new software on them and change their code down to the OS level. You can even snapshot the VM in a given state to roll it back to that configuration should there be issues later. Like containers, VMs are separate from other software on the same piece of hardware, making them perfect environments for software testing.
Because VMs allocate resources below the level of a guest OS, a malicious application that compromises one VM is unlikely to affect the host OS or access the machine’s firmware. That keeps other VMs running on the same machine safe. And, because your VM can use a different OS than its host device, you can use VMs to test software in different environments.
There are many tools available to build and manage VMs. The most essential are hypervisors, which govern access to the underlying resources for one or more VMs. Other tools help users create and manage many VMs simultaneously. Some developers use pre-configured VMs to ensure they are set up correctly and have all the basic programs they need to start.
Containers vs VMs: which should you use?
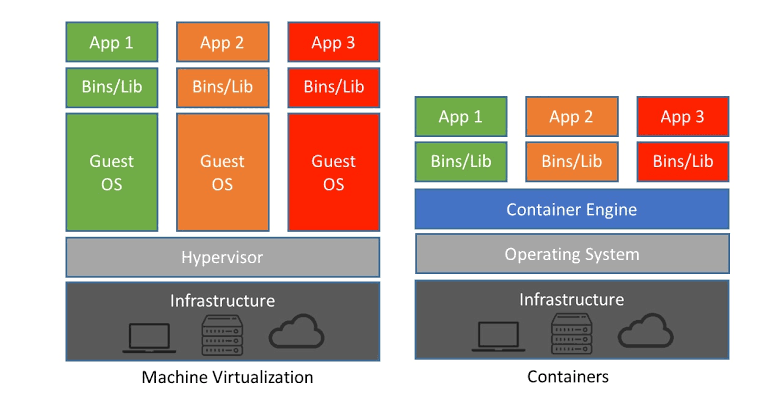
VMs and containers are both powerful technologies with specific use cases. Both provide isolated environments to run processes securely, but they differ in their specific purposes.
A containerized application has more direct access to hardware than an application running in a VM, making containers well-suited for lightweight use cases. Suppose you are looking to run a single process in multiple separate instances or run many different processes in isolation from each other. In that case, it makes sense to go with containers. Their small resource footprints make them easy to start up quickly and run at scale.
Organizations concerned about security can securely examine a container image to know what it will do before creating the container itself. That transparency makes containers easy to scan, but it comes at a price. You must scan shared containers for vulnerabilities to avoid replicating those vulnerabilities in the systems where they are used.
It is also easy to update every instance of a containerized application. You make an updated version of the container image and create new containers from that updated image. Then you can delete out-of-date and less secure containers without affecting other processes. You can even automate the update process and rely on containers’ fast start-up times to ensure that updates happen quickly every time.
Containers can make some complex tasks simpler. For example, you can build a CI/CD pipeline easily with a Docker image and a CircleCI config file. The pipeline makes it easy to quickly test an image and then push it to Docker Hub or another container registry. That lets you move quickly through the CI/CD pipeline from building to deployment.
Containers also facilitate the use of microservices. Microservices split larger applications into bite-sized processes, giving greater flexibility to users and securely separating those processes. Running microservices on a VM would involve spinning up a separate VM for every microservice, which is an inefficient allocation of resources. Or it involves running multiple services on the same VM, which loses the benefits of isolation.
Despite their popularity, containers have not replaced VMs completely. In many cases, containers complement the use of VMs. If you want to test an application that may compromise your entire OS or need to share hardware between services running on different operating systems, you need a VM. Because all your containers on a given machine share the same kernel, it is easier for malicious code to compromise the entire machine.
Because containers depend on the kernel they run on, it is challenging to implement OS-level changes from within the container. For example, suppose you want to modify a system kernel with a sysctl command from within a container. In that case, you must give the container a level of privileges that would negate any security benefits gained from isolation.
Instead, you can use a machine executor to do it from within a VM. That is possible because a VM’s OS is installed within the VM, whereas the kernel that a container depends on is outside the container.
Final Thoughts
From building to testing to deployment to vulnerability management, containers and VMs work together with your CI/CD pipeline to keep operations running smoothly.
Containers and VMs are two critical tools for virtualizing your programs. Which you use depends on what you need to do, and both make significant contributions to facilitating your CI/CD pipeline.
By combining the security of virtual machines security and the efficiency of containers, you can take advantage of all the benefits of virtualization. By using VMs to secure your applications and containers to move and deploy code between different machines, you play to both of their strengths.
🅐🅚🅖
Interested in Management, Design or Technology Consulting, contact anil.kg.26@gmail.com
Get updates and news on our social channels!
LATEST POSTS
- A Tale Of Two Frameworks: Spring Boot vs. Django
 “Spring Boot’s convention over configuration approach simplifies development, allowing developers to focus on building robust applications rather than wrestling with… Read more: A Tale Of Two Frameworks: Spring Boot vs. Django
“Spring Boot’s convention over configuration approach simplifies development, allowing developers to focus on building robust applications rather than wrestling with… Read more: A Tale Of Two Frameworks: Spring Boot vs. Django - Unleashing The Power Of Django
 “Django, akin to a Swiss Army knife, provides a comprehensive toolkit, facilitating developers in tackling diverse web development challenges with… Read more: Unleashing The Power Of Django
“Django, akin to a Swiss Army knife, provides a comprehensive toolkit, facilitating developers in tackling diverse web development challenges with… Read more: Unleashing The Power Of Django - Potential of Progressive Web Apps (PWAs)
 “PWAs are not just about technology; they are about creating meaningful connections with users.” Why PWAs Are the Next Frontier… Read more: Potential of Progressive Web Apps (PWAs)
“PWAs are not just about technology; they are about creating meaningful connections with users.” Why PWAs Are the Next Frontier… Read more: Potential of Progressive Web Apps (PWAs) - Unleashing The Power Of Spring Framework
 “Spring Framework simplifies enterprise Java development, but it does so in a way that embraces existing frameworks and infrastructure.” –… Read more: Unleashing The Power Of Spring Framework
“Spring Framework simplifies enterprise Java development, but it does so in a way that embraces existing frameworks and infrastructure.” –… Read more: Unleashing The Power Of Spring Framework - Key Trends Of OSINT In 2024
 “The future of OSINT lies in our ability to adapt and innovate. By embracing emerging technologies and ethical best practices,… Read more: Key Trends Of OSINT In 2024
“The future of OSINT lies in our ability to adapt and innovate. By embracing emerging technologies and ethical best practices,… Read more: Key Trends Of OSINT In 2024 - Can Google’s Carbon Language Replace C++?
 “While Carbon may excel in performance-critical domains, it cannot replace the versatility and extensive ecosystem of C++.” As the world… Read more: Can Google’s Carbon Language Replace C++?
“While Carbon may excel in performance-critical domains, it cannot replace the versatility and extensive ecosystem of C++.” As the world… Read more: Can Google’s Carbon Language Replace C++? - Integration of Design Thinking, Lean, and Agile
 “Innovation thrives when Design Thinking, Lean, and Agile converge, creating a powerful force that propels organizations towards excellence.” In today’s… Read more: Integration of Design Thinking, Lean, and Agile
“Innovation thrives when Design Thinking, Lean, and Agile converge, creating a powerful force that propels organizations towards excellence.” In today’s… Read more: Integration of Design Thinking, Lean, and Agile - Benefits Of Infrastructure as Code (IaC)
 “Infrastructure as Code is the single most important thing you can do to improve the agility, reliability, and security of… Read more: Benefits Of Infrastructure as Code (IaC)
“Infrastructure as Code is the single most important thing you can do to improve the agility, reliability, and security of… Read more: Benefits Of Infrastructure as Code (IaC) - Power Of Internet of Everything (IoE)
 “The true power of the Intebrnet of Everything lies not in the things themselves, but in the connections and insights… Read more: Power Of Internet of Everything (IoE)
“The true power of the Intebrnet of Everything lies not in the things themselves, but in the connections and insights… Read more: Power Of Internet of Everything (IoE) - How Is The Enterprise IoT Evolving?
 “IoT is not just about connecting things; it’s about connecting minds, creating experiences, and transforming industries.” Pavan Singh, IoT Mentor… Read more: How Is The Enterprise IoT Evolving?
“IoT is not just about connecting things; it’s about connecting minds, creating experiences, and transforming industries.” Pavan Singh, IoT Mentor… Read more: How Is The Enterprise IoT Evolving? - IT Pricing Strategy And Models
 “The art of pricing lies in finding the perfect balance between capturing value and satisfying customers.” In the ever-evolving landscape… Read more: IT Pricing Strategy And Models
“The art of pricing lies in finding the perfect balance between capturing value and satisfying customers.” In the ever-evolving landscape… Read more: IT Pricing Strategy And Models - What Is SYCL (“sickle”)?
 “SYCL provides a powerful and intuitive programming model that simplifies heterogeneous computing, allowing developers to write portable code that can… Read more: What Is SYCL (“sickle”)?
“SYCL provides a powerful and intuitive programming model that simplifies heterogeneous computing, allowing developers to write portable code that can… Read more: What Is SYCL (“sickle”)? - What Is A Data Lakehouse?
 “With a data lakehouse, organizations can break down data silos, democratize data access, and accelerate innovation by enabling data exploration… Read more: What Is A Data Lakehouse?
“With a data lakehouse, organizations can break down data silos, democratize data access, and accelerate innovation by enabling data exploration… Read more: What Is A Data Lakehouse? - 5G – The Future Of The Internet
 “5G is the next big step in the evolution of wireless technology. It will offer significantly faster speeds and lower… Read more: 5G – The Future Of The Internet
“5G is the next big step in the evolution of wireless technology. It will offer significantly faster speeds and lower… Read more: 5G – The Future Of The Internet - Ransomware Groups Are Switching To Rust
 “Rust is to Ransomware what a lockpick is to a thief – a powerful tool that can be used for… Read more: Ransomware Groups Are Switching To Rust
“Rust is to Ransomware what a lockpick is to a thief – a powerful tool that can be used for… Read more: Ransomware Groups Are Switching To Rust - Streaming Data Pipelines
 “A streaming data pipeline is like a river: it flows continuously, changes constantly, and requires monitoring to ensure it stays… Read more: Streaming Data Pipelines
“A streaming data pipeline is like a river: it flows continuously, changes constantly, and requires monitoring to ensure it stays… Read more: Streaming Data Pipelines - Why Rust Is Best?
 “Rust is a systems programming language that runs blazingly fast, prevents segfaults, and guarantees thread safety.” Rust is a modern… Read more: Why Rust Is Best?
“Rust is a systems programming language that runs blazingly fast, prevents segfaults, and guarantees thread safety.” Rust is a modern… Read more: Why Rust Is Best? - Database Sharding Explained
 “Database sharding is like breaking a large puzzle into smaller, more manageable pieces, enabling improved scalability, performance, and availability, but… Read more: Database Sharding Explained
“Database sharding is like breaking a large puzzle into smaller, more manageable pieces, enabling improved scalability, performance, and availability, but… Read more: Database Sharding Explained - Ambient Computing Will Be The Future Tech
 “Ambient computing creates a seamless technology-rich environment, but challenges in privacy, security, ethics, interoperability, user acceptance, and technical complexity must… Read more: Ambient Computing Will Be The Future Tech
“Ambient computing creates a seamless technology-rich environment, but challenges in privacy, security, ethics, interoperability, user acceptance, and technical complexity must… Read more: Ambient Computing Will Be The Future Tech - Key Trends Of OSINT In 2023
 “OSINT is not just a technique, it’s a mindset. It’s about looking at the world with an open mind and… Read more: Key Trends Of OSINT In 2023
“OSINT is not just a technique, it’s a mindset. It’s about looking at the world with an open mind and… Read more: Key Trends Of OSINT In 2023 - Why Is OSINT Important?
 “OSINT is not just a technique, it’s a mindset. It’s about looking at the world with an open mind and… Read more: Why Is OSINT Important?
“OSINT is not just a technique, it’s a mindset. It’s about looking at the world with an open mind and… Read more: Why Is OSINT Important? - DataOps Explained
 “DataOps is the practice of integrating data engineering and data analytics to enable agile development, testing, and deployment of data-driven… Read more: DataOps Explained
“DataOps is the practice of integrating data engineering and data analytics to enable agile development, testing, and deployment of data-driven… Read more: DataOps Explained - Transformation Platform as a Service (tPaaS)
 “tPaaS is all about enabling Digital Transformation by providing a platform that supports fast, agile and secure development and deployment… Read more: Transformation Platform as a Service (tPaaS)
“tPaaS is all about enabling Digital Transformation by providing a platform that supports fast, agile and secure development and deployment… Read more: Transformation Platform as a Service (tPaaS) - Hello Julia – Programming Language For Scientific Computing
 “Julia is a high-level, high-performance dynamic programming language designed for numerical computing, data science, and scientific computing.” The Julia Language… Read more: Hello Julia – Programming Language For Scientific Computing
“Julia is a high-level, high-performance dynamic programming language designed for numerical computing, data science, and scientific computing.” The Julia Language… Read more: Hello Julia – Programming Language For Scientific Computing - Top Programming Languages For Fintech
 “The top programming languages for Fintech are those that provide robust and secure frameworks for handling sensitive financial data, as… Read more: Top Programming Languages For Fintech
“The top programming languages for Fintech are those that provide robust and secure frameworks for handling sensitive financial data, as… Read more: Top Programming Languages For Fintech - How To Choose A NoSQL Database
 “SQL databases are like Excel spreadsheets. They’re good for storing structured data that you need to query in a specific… Read more: How To Choose A NoSQL Database
“SQL databases are like Excel spreadsheets. They’re good for storing structured data that you need to query in a specific… Read more: How To Choose A NoSQL Database - Zero Knowledge Proof Explained
 “Zero Knowledge Proof is a powerful cryptographic tool that enables secure and private communication without revealing sensitive information, making it… Read more: Zero Knowledge Proof Explained
“Zero Knowledge Proof is a powerful cryptographic tool that enables secure and private communication without revealing sensitive information, making it… Read more: Zero Knowledge Proof Explained - Embracing Decentralized CyberSecurity
 “Decentralized CyberSecurity moves responsibilities and controls away from the center, to the individual areas most vulnerable to attack today.” Security… Read more: Embracing Decentralized CyberSecurity
“Decentralized CyberSecurity moves responsibilities and controls away from the center, to the individual areas most vulnerable to attack today.” Security… Read more: Embracing Decentralized CyberSecurity - Global Impact of Ransomware Attacks
 “The global impact of ransomware attacks is a sobering reminder that cybersecurity is not just about protecting our data and… Read more: Global Impact of Ransomware Attacks
“The global impact of ransomware attacks is a sobering reminder that cybersecurity is not just about protecting our data and… Read more: Global Impact of Ransomware Attacks - Process Orchestrator Explained
 “Process orchestrator is the ultimate tool for achieving operational excellence, enabling you to optimize processes, improve productivity, and reduce costs.”… Read more: Process Orchestrator Explained
“Process orchestrator is the ultimate tool for achieving operational excellence, enabling you to optimize processes, improve productivity, and reduce costs.”… Read more: Process Orchestrator Explained - What Does Platform Engineering Do?
 “The success of a Digital Platform depends on the strength of its underlying engineering. Solid engineering principles ensure reliability, scalability,… Read more: What Does Platform Engineering Do?
“The success of a Digital Platform depends on the strength of its underlying engineering. Solid engineering principles ensure reliability, scalability,… Read more: What Does Platform Engineering Do? - Are Full-Stack Developers Obsolete?
 “According to the Stack Overflow 2016 Developer Survey, Full-Stack Developers are one of the highest-paid and most sought-after professionals today.”… Read more: Are Full-Stack Developers Obsolete?
“According to the Stack Overflow 2016 Developer Survey, Full-Stack Developers are one of the highest-paid and most sought-after professionals today.”… Read more: Are Full-Stack Developers Obsolete? - Top 5 Issues For Overusing Microservices
 “Microservices should only be seriously considered after evaluating the alternative paths.” The overuse of new architectural styles is common within… Read more: Top 5 Issues For Overusing Microservices
“Microservices should only be seriously considered after evaluating the alternative paths.” The overuse of new architectural styles is common within… Read more: Top 5 Issues For Overusing Microservices - Customer Experience (CX) Trends In 2023
 “Customer Experience is the next competitive battleground. It’s where business is going to be won or lost.” Tom Knighton, Executive… Read more: Customer Experience (CX) Trends In 2023
“Customer Experience is the next competitive battleground. It’s where business is going to be won or lost.” Tom Knighton, Executive… Read more: Customer Experience (CX) Trends In 2023 - Cognitive Computing In 2023 And Beyond
 “IBM defines Cognitive Computing as systems that learn at scale, reason with purpose and interact with humans naturally.” 2022 was… Read more: Cognitive Computing In 2023 And Beyond
“IBM defines Cognitive Computing as systems that learn at scale, reason with purpose and interact with humans naturally.” 2022 was… Read more: Cognitive Computing In 2023 And Beyond - Top 7 Digital Transformation Trends In 2023
 “The threat of a recession coupled with the ongoing need for transformation and growth means CIOs must make force multiplying… Read more: Top 7 Digital Transformation Trends In 2023
“The threat of a recession coupled with the ongoing need for transformation and growth means CIOs must make force multiplying… Read more: Top 7 Digital Transformation Trends In 2023 - Top 5 DevOps Trends in 2023
 “The Global DevOps market size is expected to expand at a CAGR of 24.59% by 2027, reaching over 22199.4 million… Read more: Top 5 DevOps Trends in 2023
“The Global DevOps market size is expected to expand at a CAGR of 24.59% by 2027, reaching over 22199.4 million… Read more: Top 5 DevOps Trends in 2023 - Top 5 Cybersecurity Predictions For 2023
 “Cybersecurity will continue to be a major focus for company leaders as they bolster their digital defenses in 2023 and… Read more: Top 5 Cybersecurity Predictions For 2023
“Cybersecurity will continue to be a major focus for company leaders as they bolster their digital defenses in 2023 and… Read more: Top 5 Cybersecurity Predictions For 2023 - Top 5 Cloud Computing Trends In 2023
 “Cloud Computing has been one of the most critical technologies of the last decade.” The ongoing mass adoption of Cloud… Read more: Top 5 Cloud Computing Trends In 2023
“Cloud Computing has been one of the most critical technologies of the last decade.” The ongoing mass adoption of Cloud… Read more: Top 5 Cloud Computing Trends In 2023 - 10 Technology Trends For 2023
 What are the best new technologies to learn to improve your career and knowledge? Technology today is evolving at a… Read more: 10 Technology Trends For 2023
What are the best new technologies to learn to improve your career and knowledge? Technology today is evolving at a… Read more: 10 Technology Trends For 2023 - Top 5 AI /ML Trends In 2023
 “AI continues to transform our world as companies look to win over consumers with intelligent experiences delivered in real time… Read more: Top 5 AI /ML Trends In 2023
“AI continues to transform our world as companies look to win over consumers with intelligent experiences delivered in real time… Read more: Top 5 AI /ML Trends In 2023 - Android Runs Better When Covered In Rust
 “C/C++ should no longer be used to start new projects and that Rust should be deployed where a language without… Read more: Android Runs Better When Covered In Rust
“C/C++ should no longer be used to start new projects and that Rust should be deployed where a language without… Read more: Android Runs Better When Covered In Rust - Cybersecurity Mesh Architecture (CSMA)
 “CSMA is geared toward simplifying security architecture by encouraging collaboration and integration of a corporate security architecture.” One of the… Read more: Cybersecurity Mesh Architecture (CSMA)
“CSMA is geared toward simplifying security architecture by encouraging collaboration and integration of a corporate security architecture.” One of the… Read more: Cybersecurity Mesh Architecture (CSMA) - Data Mesh And It’s Principles
 “Data Mesh is a strategic approach to modern data management and a way to strengthen an organization’s digital transformation journey,… Read more: Data Mesh And It’s Principles
“Data Mesh is a strategic approach to modern data management and a way to strengthen an organization’s digital transformation journey,… Read more: Data Mesh And It’s Principles - Hard Tech To Disrupt The Future
 “Affordable robotics, AI-driven sensor fusion, uninterrupted connectivity and supermaterials are merging into the technology stack to unlock massive new tranches… Read more: Hard Tech To Disrupt The Future
“Affordable robotics, AI-driven sensor fusion, uninterrupted connectivity and supermaterials are merging into the technology stack to unlock massive new tranches… Read more: Hard Tech To Disrupt The Future - Top 5 Cloud Computing Vulnerabilities
 “Protecting your organization requires accepting the fact that your systems will be breached at some point; therefore, your strategy should… Read more: Top 5 Cloud Computing Vulnerabilities
“Protecting your organization requires accepting the fact that your systems will be breached at some point; therefore, your strategy should… Read more: Top 5 Cloud Computing Vulnerabilities - What’s Next After Cloud Computing – Edge?
 “Now, some companies are looking to replace Cloud Computing with something called Sky, Edge, or Hybrid Computing.” In the past few… Read more: What’s Next After Cloud Computing – Edge?
“Now, some companies are looking to replace Cloud Computing with something called Sky, Edge, or Hybrid Computing.” In the past few… Read more: What’s Next After Cloud Computing – Edge? - Chip To Cloud IoT
 “Chip-to-Cloud IoT looks like a promising way to .build a more secure, useful and decentralized technology for all.” Shannon Flynn… Read more: Chip To Cloud IoT
“Chip-to-Cloud IoT looks like a promising way to .build a more secure, useful and decentralized technology for all.” Shannon Flynn… Read more: Chip To Cloud IoT - How To Secure The Cloud
 “Encryption, Configuration are one of the best ways to secure your Cloud Computing systems.’ Fortunately, there is a lot that you… Read more: How To Secure The Cloud
“Encryption, Configuration are one of the best ways to secure your Cloud Computing systems.’ Fortunately, there is a lot that you… Read more: How To Secure The Cloud - Top 7 Advanced Cloud Security Challenges
 “Before jumping feet-first into the Cloud, understand the new and continuing top Cloud Security challenges your organization is likely to… Read more: Top 7 Advanced Cloud Security Challenges
“Before jumping feet-first into the Cloud, understand the new and continuing top Cloud Security challenges your organization is likely to… Read more: Top 7 Advanced Cloud Security Challenges - Why Cloud Security Is Important
 “Cloud Security is the whole bundle of technology, protocols, and best practices that protect Cloud Computing environments, applications running in… Read more: Why Cloud Security Is Important
“Cloud Security is the whole bundle of technology, protocols, and best practices that protect Cloud Computing environments, applications running in… Read more: Why Cloud Security Is Important - Why Implement Zero Trust Security Model?
 “Zero Trust extends the principle of ‘least privilege’ to its ultimate conclusion: Trust no one and grant the least privilege,… Read more: Why Implement Zero Trust Security Model?
“Zero Trust extends the principle of ‘least privilege’ to its ultimate conclusion: Trust no one and grant the least privilege,… Read more: Why Implement Zero Trust Security Model? - Advantages And Disadvantages Of Cloud Computing
 “When weighing the Cloud Computing advantages and disadvantages, it’s important to keep the sources of those pros and cons in… Read more: Advantages And Disadvantages Of Cloud Computing
“When weighing the Cloud Computing advantages and disadvantages, it’s important to keep the sources of those pros and cons in… Read more: Advantages And Disadvantages Of Cloud Computing - Benefits Of Cloud Computing
 “Cloud Computing benefits organizations in many ways. In fact, the benefits are so numerous that it makes it almost impossible not… Read more: Benefits Of Cloud Computing
“Cloud Computing benefits organizations in many ways. In fact, the benefits are so numerous that it makes it almost impossible not… Read more: Benefits Of Cloud Computing - Why WebAssembly Is The Future Of Computing?
 “WebAssembly is a binary instruction format and virtual machine that brings near-native performance to web browser applications, and allows developers… Read more: Why WebAssembly Is The Future Of Computing?
“WebAssembly is a binary instruction format and virtual machine that brings near-native performance to web browser applications, and allows developers… Read more: Why WebAssembly Is The Future Of Computing? - Virtualization In Cloud Computing
 “Virtualization and Cloud Computing are often discussed interchangeably, but while they’re closely associated, these tech terms have crucial differences.” Virtualization… Read more: Virtualization In Cloud Computing
“Virtualization and Cloud Computing are often discussed interchangeably, but while they’re closely associated, these tech terms have crucial differences.” Virtualization… Read more: Virtualization In Cloud Computing - Cloud Service And Deployment Models
 “I don’t need a hard disk in my computer if I can get to the server faster… carrying around these… Read more: Cloud Service And Deployment Models
“I don’t need a hard disk in my computer if I can get to the server faster… carrying around these… Read more: Cloud Service And Deployment Models - Why Use Serverless Computing
 “Serverless Computing is a Cloud computing execution model that lets software developers build and run applications and servers without having… Read more: Why Use Serverless Computing
“Serverless Computing is a Cloud computing execution model that lets software developers build and run applications and servers without having… Read more: Why Use Serverless Computing - Spatial Computing Revolutionizing Our World
 “Today, new technologies are advancing at dizzying speeds –impacting all areas of our lives, including how we shop and pay… Read more: Spatial Computing Revolutionizing Our World
“Today, new technologies are advancing at dizzying speeds –impacting all areas of our lives, including how we shop and pay… Read more: Spatial Computing Revolutionizing Our World - Trending Fullstack Frameworks
 “Writing the first 90 percent of a computer program takes 90 percent of the time. The remaining ten percent also… Read more: Trending Fullstack Frameworks
“Writing the first 90 percent of a computer program takes 90 percent of the time. The remaining ten percent also… Read more: Trending Fullstack Frameworks - Threat Intelligence Explained
 “Threat intelligence is evidence-based knowledge about an existing or emerging menace or hazard to assets that can be used to… Read more: Threat Intelligence Explained
“Threat intelligence is evidence-based knowledge about an existing or emerging menace or hazard to assets that can be used to… Read more: Threat Intelligence Explained - Docker’s Role In Microservices
 “Docker is an open platform for developing, shipping, and running applications. Docker enables you to separate your applications from your… Read more: Docker’s Role In Microservices
“Docker is an open platform for developing, shipping, and running applications. Docker enables you to separate your applications from your… Read more: Docker’s Role In Microservices - Why Is Kafka The First Choice For Microservices?
 “Kafka is an event streaming platform used for reading and writing data that makes it easy to connect Microservices.’ When… Read more: Why Is Kafka The First Choice For Microservices?
“Kafka is an event streaming platform used for reading and writing data that makes it easy to connect Microservices.’ When… Read more: Why Is Kafka The First Choice For Microservices? - Pros And Cons Of Microservices Architecture
 “Microservices Architecture has become increasingly popular in recent years. It offers a number of advantages over traditional monolithic architectures, but… Read more: Pros And Cons Of Microservices Architecture
“Microservices Architecture has become increasingly popular in recent years. It offers a number of advantages over traditional monolithic architectures, but… Read more: Pros And Cons Of Microservices Architecture


[…] Containers are an excellent example of Microservices Architecture as they allow businesses to focus on developing services without worrying about dependencies. Cloud-native applications are commonly built as microservices by leveraging containers. […]
LikeLike
[…] Because the Public cloud does not have clear perimeters, it presents a fundamentally different security reality. This becomes even more challenging when adopting modern Cloud approaches such as automated Continuous Integration and Continuous Deployment (CI/CD) methods, distributed serverless architectures, and ephemeral assets like Functions as a Service and containers. […]
LikeLike